Competition is almost inevitable in business and as a key driver of innovation, that’s mostly a good thing. Unfair competition, on the other hand, is rarely considered a plus.
Competition is almost inevitable in business and as a key driver of innovation, that’s mostly a good thing. Unfair competition, on the other hand, is rarely considered a plus.
In a complaint filed in a California court this week, adult entertainment company TIR Consulting LLC says that it faces unfair and illegal competition from pirate sites. It’s a familiar story for rightsholders everywhere but this lawsuit is far from ordinary.
TIR’s Enforcement Efforts Fail
Since 2015, TIR has made its specialist content available via the website mistressharley.com (NSFW) and through authorized third parties under licensing agreements.
In parallel, websites that sell pirated copies of TIR’s copyrighted videos compete in the same market by targeting TIR’s customers. Some use confusingly similar domains that are designed to mislead potential customers, TIR says.
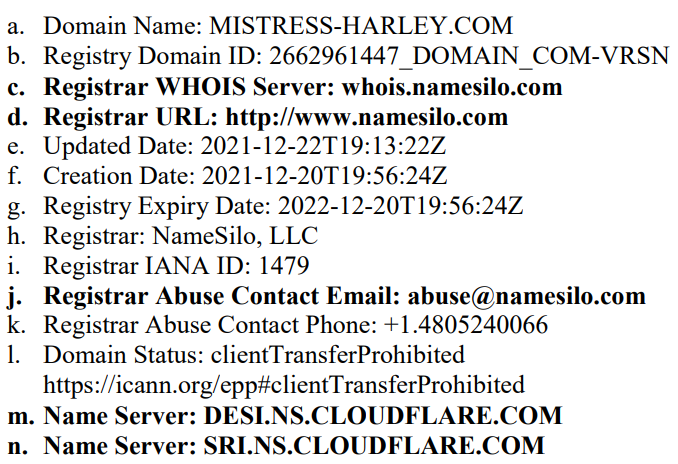
The complaint notes that at least two of these pirate sites use privacy services provided by the named defendants – Cloudflare and domain company NameSilo.
TIR claims that enforcing its rights is all but impossible due to these privacy services. As a result, Cloudflare and NameSilo must be held liable for the infringements of their customers, along with Does 1-100 who are also liable in some way or another.
65 Videos in Total
The complaint lists 65 URLs (“infringing links”) on the alleged pirate site mistress-harley.com. These same 65 URLs are said to “backlink” to manyvips.com but specific URLs are not listed in the complaint. The listed URLs appear to reference video content, but TIR uses trademark terminology instead.
“Each of the 65 Infringing Links reflects the registered family of trademarks for
‘Mistress Harley’ all of which are owned exclusively by TIR,” the complaint reads.
TIR further blends copyright and trademark law by claiming that Cloudflare “admitted that the accepted 65 URL(s) for the DMCA report on mistress-harley.com” includes the 65 “infringing links” referenced earlier under trademark law.
The adult company later states that while its complaint covers 65 videos “made, paid for, produced and owned by TIR,” just four have been registered with the US Copyright Office.
“No Interference with Anonymity”
TIR says that pirate sites pay Cloudflare for “housing services” and a “guarantee that CloudFlare will do nothing to interfere with their anonymity and their cyber-theft.”
According to the complaint, Cloudflare provides services to mistress-harley.com.
TIR says that pirates are able to sell copies of its videos on “domain sites” hosted by companies that sell and host domains, while “guaranteeing the anonymity of domain owners.” In this case, NameSilo is called out for offering a “free WHOIS privacy” service, which is used by mistress-harley.com and a second unlicensed platform, manyvips.com.
“There is no question that this is not just an attractive service, but a necessary
service for a pirate that wants to set up a site with illegal downloads,” the complaint notes.
“Cloudflare – A Favored Tool For Infringers”
After a rundown of services provided by Cloudflare, the complaint highlights the company’s privacy pledge: “[A]ny personal information you provide to us is just that: personal and private.”
Cloudflare’s claim that it has never modified the intended destination of DNS responses “at the request of law enforcement or another third party” is also mentioned.
The natural consequence of the above, TIR concludes, is that “CloudFlare is a safe holding space for website owners who are offering illegal content, and both sides know exactly what is being bought and sold.”
TIR, Cloudflare and the ‘Mon Cheri’ Decision
While bold, TIR’s allegations are nothing new. In 2018, Mon Cherie Bridals sued Cloudflare for failing to terminate customers identified as repeat infringers. The case was a pretty big deal and after three years of litigation,
Cloudflare took the win
and an important ruling on liability.
The Mon Cherie decision is referenced in TIR’s complaint, but not in recognition of Cloudflare’s win. Instead, a statement made by Judge Chhabria in the earlier case (italics, below) is framed as undermining Cloudflare’s position.
If Cloudflare’s provision of these services made it more difficult for a third party to report incidents of infringement to the web host as part of an effort to get the underlying content taken down, perhaps it could be liable for contributory infringement
While TIR notes that the above is “precisely the basis for the claims” in this complaint, in Mon Cherie the Judge said that Cloudflare’s actions did not incur liability.
Cloudflare Disclosure Led Back to NameSilo
Since Cloudflare forwards DMCA notices to site hosts and informs complainants of the identity of the host, Judge Chhabria concluded in Mon Cherie that Cloudflare doesn’t make it harder to go after pirate sites.
Indeed, the TIR complaint acknowledges that Cloudflare identified mistress-harley.com’s hosting provider (SECUNET, BG) and provided an abuse contact email address (abuse@cryptoservers.biz).
When TIR sent a trademark/copyright complaint to the host but received no response, the adult company did a WHOIS lookup for cryptoservers.biz. It revealed NameSilo as the domain registrar and PrivacyGuardian.org protecting the registrant’s details.
In response to a formal complaint, NameSilo’s abuse team reminded TIR that “..we are only the domain name registrar and cannot validate or control the content posted on the site.” PrivacyGuard’s policy advised TIR that in the event of a copyright or trademark dispute, “you should direct your complaint to the respective web site host for the domain.”
‘Pirate’ Mistress-Harley Still Active
With Cloudflare reportedly offering similar advice to target the host itself, TIR appears to have lost patience and filed this complaint.
“As a result of the piracy and infringement, TIR has suffered consistent lost profits and decreased sales, and has calculated this lost amount to be in the tens of thousands of dollars and growing exponentially every day,” the company notes.
“This case raises the problem of service providers who continue to do commerce with pirate sites even after receipt of actual knowledge of repetitive acts of infringement on such sites. These Defendants profit by supporting and providing critical services to pirate sites despite being on notice that these customers are repeat infringers.”
TIR says that Cloudflare and NameSilo “systematically failed to implement or enforce a repeat infringer policy” in the knowledge that many “lawful copyright and trademark holders” can’t afford to fight legal battles.
“This undermines the entire purpose of DMCA,” the company adds.
Causes of Action
Since Cloudflare and NameSilo will undoubtedly respond to these claims in some detail, we’ll cover their responses in due course. In the meantime, the brief list below is included for reference, including links to law exactly as cited in the complaint.
1- Contributory Trademark Infringement –
15 U.S.C. § 1114
Cloudflare/NameSilo
2- Direct Trademark Infringement – (U.S.C. Not listed) Cloudflare, NameSilo, Does 1-100
3- Not listed/absent from the complaint
4- Contributory Copyright Infringement –
15 U.S.C. § 1125(a)
Cloudflare/NameSilo
5- Vicarious Copyright Infringement –
15 U.S.C. § 1125(a)
Cloudflare/NameSilo
6- Direct Copyright Infringement –
15 U.S.C. § 1125(a)
Cloudflare/NameSilo/Does 1-100
7- Unfair Competition – (
link
) Cloudflare/NameSilo
At the time of writing, Cloudflare does not ‘protect’ mistress-harley.com’s server in any way.
TIR’s complaint against Cloudflare, NameSilo & Does 1-100 (
pdf
)
From:
TF
, for the latest news on copyright battles, piracy and more.
 chevron_right
chevron_right