 Day in and day out, dozens of new movies and TV shows leak online. It’s become so normal that most pirates take it for granted.
Day in and day out, dozens of new movies and TV shows leak online. It’s become so normal that most pirates take it for granted.
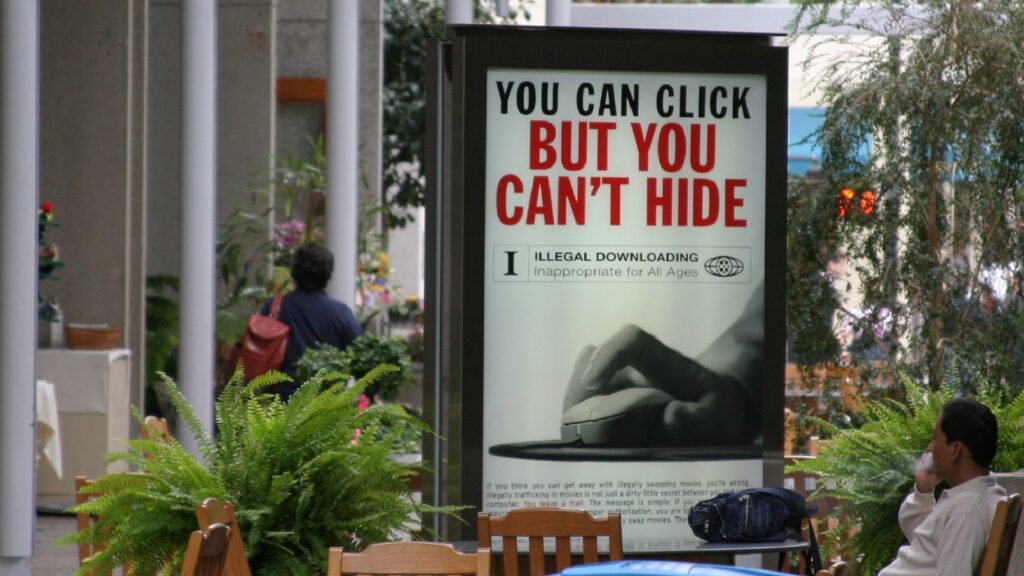
While millions of people consume this content, only a few people know who supplies it. This secrecy is much needed, as members of release groups risk criminal prosecution and multi-year prison sentences.
EVO Goes Quiet
This threat became salient again a few days ago when prolific release group EVO stopped sharing new uploads. A few days or even weeks between releases is normal for many groups but for EVO it’s highly unusual. The potential for something serious happening behind the scenes is certainly not out of the question.
Another factor to consider is that EVO is not alone; release group iFT has also stopped uploading new content recently. Both groups are connected to private torrent trackers where they release content first so their unexplained absence has quite a few people worried.
Over the past few days we have seen a wide variety of anonymous rumors and claims. According to some, EVO has been busted, but there is no evidence that officially confirms that. The only thing we know for sure is that EVO is a prime target for Hollywood and that carries risks.
EVO’s High Profile Screener Leaks
Despite its high profile, EVO hasn’t shunned the piracy limelight in recent years. The P2P release group has leaked many prominent movies, including advance screener copies of “Nomadland”, “Uncut Gems” “The Power of the Dog“ and “My Salinger Year”.
While some groups prefer to stay away from screener leaks because of the inherent risks, EVO has repeatedly claimed first place when ‘screener piracy season’ begins.
The group was also responsible for publishing an
early Blu-Ray copy
of ‘Spider-Man: No Way Home’. In addition, it shared “Dune” with its pirate audience
before the film was available
via HBO Max and US theaters.
A Hobby
When we
interviewed
the group a few months ago, they told us that money isn’t their motivation. EVO said that they leaked movies “for fun” and to help people with limited means.
“We don’t get any profit at all from this ‘hobby’. We do it for fun,” EVO informed us, adding that they like to help people. “We know we are helping lots of people that can’t afford to go to theaters.”
EVO also pointed a finger at Hollywood for making it quite expensive for people to enjoy films. EVO suggested that increased fragmentation of the streaming landscape, with every service pushing its own exclusive releases, helps to keep piracy relevant.
“Maybe, if studios would care a bit more about the consumer, there wouldn’t be much piracy on the internet. But they don’t care anymore, what matters is profit, profit and profit.
“If you are an average person these days, basically, either you are rich or you are fucked. It’s Disney+, its Netflix, its Prime, its Paramount+. God knows what else they come up with,” EVO added.
Where’s EVO?
TorrentFreak reached out to EVO over the weekend but the group didn’t respond. This means that the mystery and rumors will likely continue, at least until the group returns or more information becomes available.
There is no evidence to confirm that law enforcement is involved in any way but if that’s the case, it wouldn’t be the first time that a release group has been brought down.
Two years ago, U.S. law enforcement
indicted several members
of the Scene release group SPARKS. This action spooked the entire Scene and to date has resulted in the conviction of one member.
In 2011, the notorious IMAGiNE movie piracy group was
dismantled by the feds
. The group released large numbers of movies onto the Internet, many of which were still playing in theaters.
This attracted the attention of the MPA which launched an investigation. This led to the arrest and prosecution of four U.S. residents, who received sentences ranging from 23 months up to five years in prison.
From:
TF
, for the latest news on copyright battles, piracy and more.
chevron_right





 Day in and day out, dozens of new movies and TV shows leak online. It’s become so normal that most pirates take it for granted.
Day in and day out, dozens of new movies and TV shows leak online. It’s become so normal that most pirates take it for granted.
